A group of cryptocurrency threat actors dubbed “GreedyBear” has stolen over $1 million in what researchers describe as an industrial-scale campaign spanning malicious browser extensions, malware, and scam websites.
Summary
- GreedyBear has reportedly stolen over $1 million through malicious extensions, malware, and scam websites.
- More than 650 malicious tools targeting cryptocurrency wallet users were identified in the campaign.
- Researchers found signs of AI-generated code used to scale and diversify attacks.
GreedyBear has “redefined industrial-scale crypto theft,” according to Koi Security researcher Tuval Admoni, who said the group’s approach blends multiple proven attack methods into one coordinated operation.
While most cybercriminal outfits specialize in a single vector, such as phishing, ransomware, or fake extensions, GreedyBear has pursued all three simultaneously at a large scale.
The findings come just days after blockchain security firm PeckShield reported a sharp rise in crypto crime in July, with bad actors stealing roughly $142 million across 17 major incidents.
Malicious browser extensions
Koi Security’s investigation found that GreedyBear’s current campaign has already deployed more than 650 malicious tools targeting cryptocurrency wallet users.
Admoni noted that this marks an escalation from the group’s earlier “Foxy Wallet” campaign, which in July exposed 40 malicious Firefox extensions.
The group uses a technique Koi calls “Extension Hollowing” to bypass marketplace checks and gain user trust.
Operators first publish innocuous-looking Firefox extensions — such as link sanitizers or video downloaders — under new publisher accounts. These are then padded with fake positive reviews before being converted into wallet-impersonating tools targeting MetaMask, TronLink, Exodus, and Rabby Wallet.
Once weaponized, the extensions harvest credentials directly from user input fields and transmit them to GreedyBear’s command-and-control server.
Crypto Malware
Beyond extensions, researchers found nearly 500 malicious Windows executables tied to the same infrastructure.
These files span multiple malware families, including credential stealers such as LummaStealer, ransomware variants resembling Luca Stealer, and generic trojans likely acting as loaders for other payloads.
Koi Security noted that many of these samples appear in malware distribution pipelines hosted on Russian-language websites that offer cracked, pirated, or “repacked” software. This distribution method not only widens the group’s reach to less security-conscious users but also allows them to seed infections beyond the crypto-native audience.
Researchers also found malware samples that demonstrated modular capabilities, suggesting the operators can update payloads or swap functions without deploying entirely new malware.
Scam crypto services
Running in parallel with these malware operations, GreedyBear maintains a network of scam websites that impersonate cryptocurrency products and services. These websites are designed to harvest sensitive information from unsuspecting users.
Koi Security found fake landing pages advertising hardware wallets, and bogus wallet-repair services claiming to fix popular devices like Trezor. Other pages were found to be promoting fake digital wallets or crypto utilities, all with professional-grade design.
Unlike traditional phishing sites that mimic exchange login pages, these scams pose as product showcases or support services. Visitors are lured into entering wallet recovery phrases, private keys, payment information, or other sensitive data, which the attackers then exfiltrate for follow-on theft or credit card fraud.
Koi’s investigation found that some of these domains were still active and harvesting data, while others appeared dormant but ready for activation in future campaigns.
A central node
Further, Koi found that nearly all domains connected to GreedyBear’s extensions, malware, and scam websites resolve to a single IP address — 185.208.156.66.
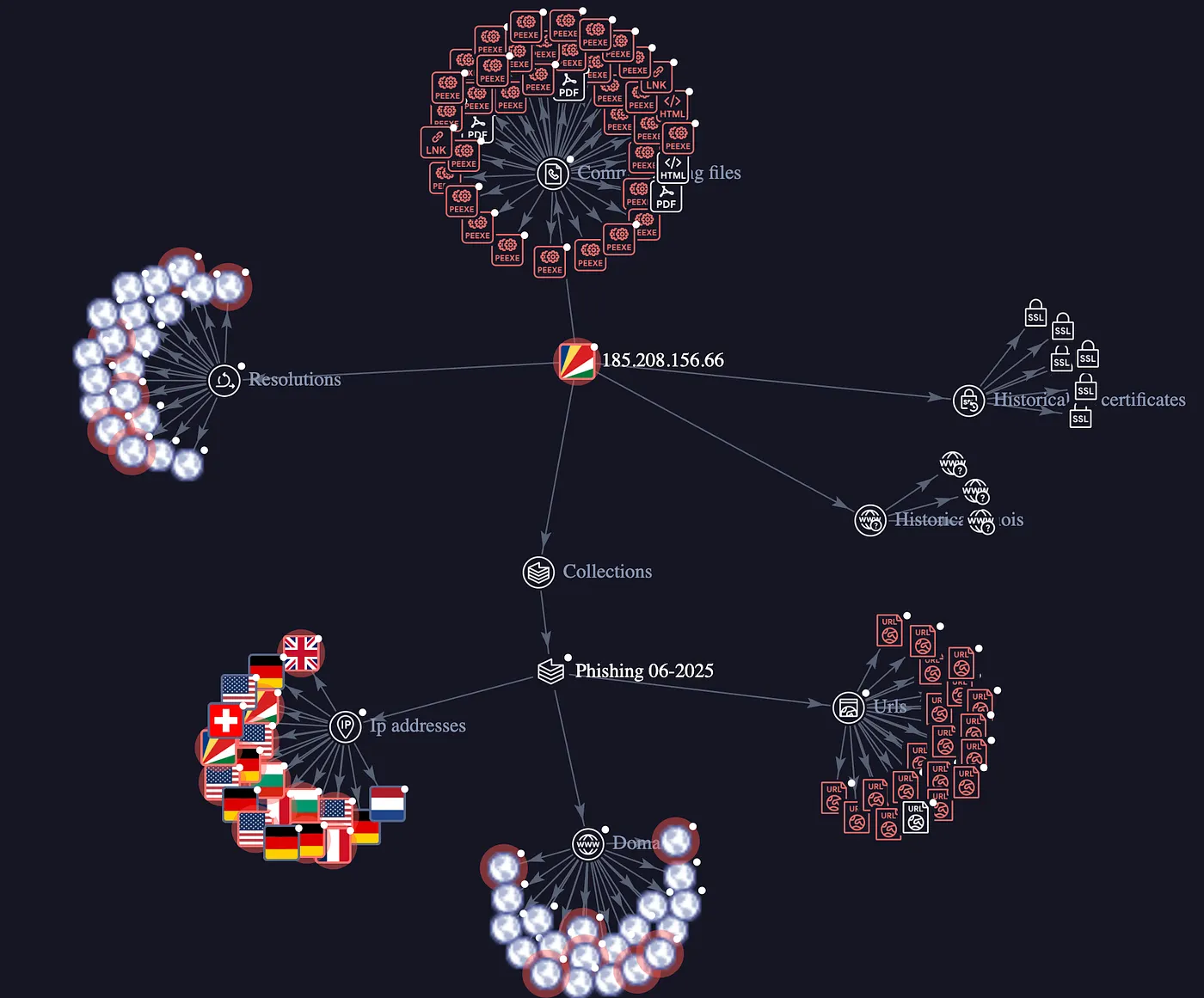
This server functions as the operation’s command-and-control hub, managing credential collection, ransomware coordination, and hosting for fraudulent websites. By consolidating operations on one infrastructure, the group is able to track victims, adjust payloads, and distribute stolen data with greater speed and efficiency.
According to Admoni, there were also signs of “AI-generated artifacts” found within the campaign’s code, which makes it “faster and easier than ever for attackers to scale operations, diversify payloads, and evade detection.”
“This isn’t a passing trend — it’s the new normal. As attackers arm themselves with increasingly capable AI, defenders must respond with equally advanced security tools and intelligence,” Admoni said.