Decentralized finance protocol SIR.trading has suffered a catastrophic exploit, losing its entire total value locked (TVL) and prompting its founder to publicly offer a $100,000 bounty in exchange for the return of the remaining stolen funds.
The attack, which drained approximately $355,000 from the platform, has raised new concerns about Ethereum’s recent Dencun upgrade.
On March 31, Xatarrer, the anonymous founder of SIR.trading, made an on-chain plea to the hacker.
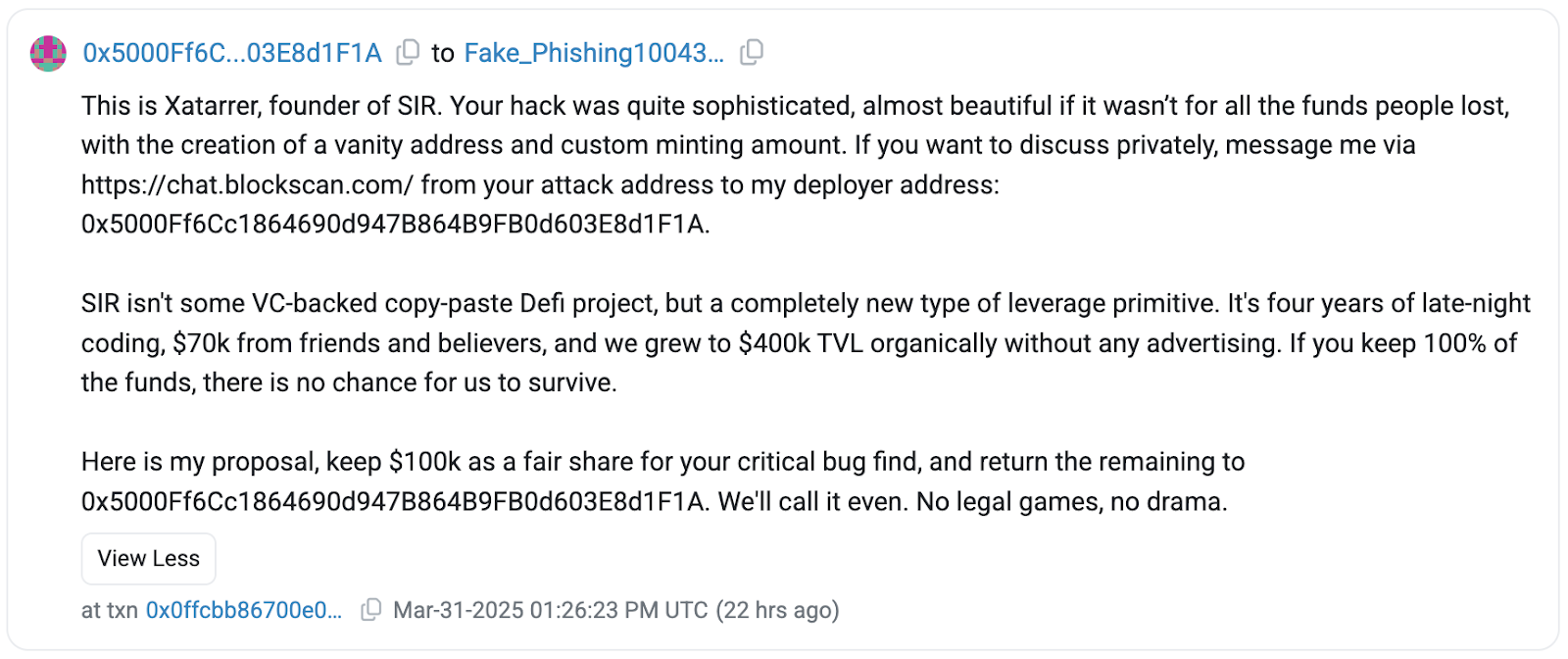
Acknowledging the skill involved in the attack, he described it as “almost beautiful” despite the devastating financial losses.
The message offered the attacker a chance to keep $100,000 as a reward for discovering the exploit while requesting that the remainder be returned.
Xatarrer emphasized that SIR.trading was not a VC-backed project but a grassroots effort built over four years, with $70,000 in funding from friends and supporters.
He stated that the platform would not survive without the stolen funds. So far, the attacker has not responded to the plea.
According to on-chain data, the stolen assets have already been funneled through Railgun, a privacy protocol designed to obscure transaction trails, making fund recovery more challenging.
The Exploit: A Clever Manipulation of Transient Storage
The vulnerability that led to the SIR.trading exploit was tied to Ethereum’s transient storage, a feature introduced in the Dencun upgrade.
This attack, described by blockchain security experts as highly sophisticated, exploited a function within SIR.trading’s Vault contract known as `uniswapV3SwapCallback`.
According to Decurity, a blockchain security firm that analyzed the exploit, the attacker leveraged transient storage to manipulate how transactions were verified within the contract.
Instead of ensuring that only legitimate Uniswap pools could execute swaps, the contract was tricked into trusting a fake Uniswap pool address controlled by the hacker.
This was made possible because transient storage resets only after a transaction concludes, allowing the attacker to modify security parameters mid-execution.
Further analysis by blockchain researcher Yi revealed that the attacker brute-forced a vanity address, ensuring it matched the contract’s expected parameters.
This enabled them to drain all assets from SIR.trading’s vault, wiping out its entire TVL.
Xatarrer acknowledged the devastating nature of the attack, calling it “the worst news a protocol could receive.”
Despite the losses, he expressed determination to rebuild, asking the community for input on possible next steps.
A Growing Trend of DeFi Exploits
The SIR.trading exploit is part of a broader trend of increasing security breaches within the decentralized finance sector.
Just six days before the attack on SIR.trading, another major exploit targeted the decentralized lending protocol Abracadabra.Money, leading to a $13 million loss.
The Abracadabra exploit, detected on March 25 by PeckShield, specifically targeted pools utilizing GMX tokens.
Attackers drained 6,260 ETH by exploiting vulnerabilities in Abracadabra’s smart contract infrastructure.
This marked the platform’s second major breach in 2024, following a $6.49 million loss in January that caused its Magic Internet Money (MIM) stablecoin to debug.
Similarly, in February 2024, the crypto sector saw losses of approximately $1.53 billion, a staggering 1,500% increase from January’s reported losses of $98 million.
The single biggest loss was caused by Bybit’s February 21 hack, which was attributed to North Korea’s Lazarus Group.
The exploit siphoned approximately $1.4 billion, making it one of the largest cryptocurrency hacks in history.
As it stands now, while Xatarrer remains hopeful that the hacker will accept the bounty offer, the reality is that many of these stolen funds may never be recovered.
The post SIR.trading Offers $100K Bounty to Exploiter After Losing Entire TVL appeared first on Cryptonews.



 ^
^ ) (@leveragesir)
) (@leveragesir) 
